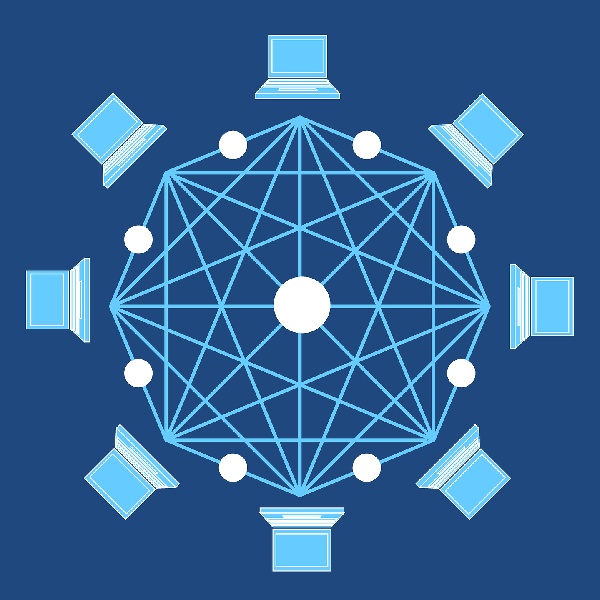
Consensus mechanisms are fundamental to the security and integrity of blockchain networks. They ensure that transactions are validated and added to the blockchain in a trustless and tamper-proof manner. However, different consensus mechanisms have varying security considerations. In this article, we will explore the security aspects of popular consensus mechanisms used in blockchain technology.
Introduction to Consensus Mechanisms
Consensus mechanisms play a vital role in ensuring the security and trustworthiness of blockchain networks. They establish agreement among participants regarding the validity and order of transactions. Let’s delve into the details of popular consensus mechanisms and their associated security considerations.
Proof of Work (PoW)
PoW, the consensus mechanism introduced by Bitcoin, relies on computational puzzles to validate transactions. While PoW is known for its robustness, it is not without security considerations. The main security concerns with PoW include the possibility of a 51% attack, where a single entity or group controls the majority of the network’s computational power, and the potential for eclipse attacks, where an attacker isolates a node from the network and manipulates its view of the blockchain.
Proof of Stake (PoS)
PoS is an alternative consensus mechanism that selects validators based on their stake in the network. While PoS offers energy efficiency and scalability, it also poses security challenges. One significant concern is the “nothing-at-stake” problem, where validators can potentially validate conflicting blocks simultaneously, leading to a fork in the blockchain. Additionally, the concentration of wealth among a few validators may raise centralization risks.
Delegated Proof of Stake (DPoS)
DPoS combines the advantages of PoW and PoS by introducing a limited number of elected delegates who validate transactions. Although DPoS enhances scalability and transaction throughput, it has security considerations. One major concern is the potential for collusion among delegates, where a group of validators conspires to manipulate the blockchain. Additionally, the governance structure of DPoS networks requires careful attention to prevent centralization risks.
Practical Byzantine Fault Tolerance (PBFT)
PBFT is a consensus mechanism suitable for permissioned blockchain networks. It achieves consensus through multiple rounds of communication and voting among network nodes. While PBFT offers fast transaction confirmation and fault tolerance, it faces security challenges. It assumes that the majority of network nodes are honest, making the system vulnerable to attacks when a significant number of nodes are malicious or compromised.
Directed Acyclic Graph (DAG)
DAG-based consensus mechanisms, such as those used by cryptocurrencies like IOTA, offer scalability and high transaction throughput. However, DAG-based networks are susceptible to security threats. One primary concern is the potential for double spending, where an attacker attempts to spend the same funds in multiple transactions. Additionally, long-range attacks, where an attacker rebuilds a different branch of the DAG, can compromise the integrity of the blockchain.
Security Considerations in Consensus Mechanisms
When evaluating the security of consensus mechanisms, several key considerations arise:
1. Attack Resistance
Consensus mechanisms must be resistant to various attacks, including Sybil attacks, where an attacker controls multiple identities to gain influence, and 51% attacks, where a single entity gains majority control over the network’s resources.
2. Network Security
Maintaining network security is crucial to prevent attacks like double spending, where an attacker attempts to spend the same funds twice, and long-range attacks, where an attacker rebuilds a different branch of the blockchain from a distant point in time. Eclipse attacks, which isolate and manipulate nodes’ views, also pose a risk.
3. Decentralization and Governance
Consensus mechanisms should strive to maintain decentralization to prevent centralization risks. Effective governance structures are essential to prevent collusion, corruption, and concentration of power among validators or delegates.
By carefully considering these security aspects, blockchain networks can mitigate risks and ensure the robustness of their consensus mechanisms.
Proof of Burn (PoB)
Proof of Burn is a unique consensus mechanism that introduces security considerations distinct from other mechanisms. Since participants “burn” their cryptocurrencies, they face potential risks associated with the irreversible nature of burning tokens. The security of PoB relies on ensuring that participants follow the correct burning process and that the burned tokens cannot be retrieved or manipulated by malicious actors. Proper verification mechanisms and cryptographic protocols are essential to prevent fraud and ensure the integrity of the burning process.
Proof of Capacity (PoC)
Proof of Capacity introduces its own set of security considerations. As miners allocate disk space for storing precomputed solutions, the security of PoC heavily depends on the protection of this storage space. Safeguarding against unauthorized access, tampering, or theft is crucial to maintain the integrity of the consensus mechanism. Encryption and robust access control mechanisms are vital to prevent malicious actors from compromising the stored solutions and manipulating the validation process.
Proof of Identity (PoI)
Security considerations in Proof of Identity mechanisms revolve around identity verification and protection against identity theft or impersonation. To ensure the security of PoI, robust identity verification processes are necessary. Techniques such as multi-factor authentication, biometrics, and cryptography can be employed to establish and verify participants’ identities securely. Additionally, mechanisms should be in place to detect and prevent identity theft, ensuring that only genuine and authorized individuals can participate in the consensus process.
Blockchain Interoperability
Security considerations in blockchain interoperability revolve around data integrity, privacy, and consensus integrity across different blockchain networks. Secure communication channels and protocols are essential to prevent tampering or interception of data during the interoperability process. Privacy-preserving techniques, such as zero-knowledge proofs or secure multiparty computation, can help protect sensitive information shared between blockchains. Ensuring the integrity and validity of transactions across interconnected blockchains requires careful design and auditing of the interoperability protocols and mechanisms.
The Role of Sharding
Sharding introduces unique security considerations to blockchain networks. Partitioning the blockchain into shards requires robust mechanisms to prevent attacks targeting specific shards. Ensuring data consistency and preventing data leakage between shards is critical. Techniques such as encryption, cross-validation of transactions across shards, and secure communication channels are crucial to maintaining the security and integrity of the sharded blockchain network.
Blockchain-based Energy Solutions
Security considerations in blockchain-based energy solutions encompass data privacy, secure energy trading, and protection against malicious actors. Ensuring the privacy of energy-related data is essential to prevent unauthorized access or manipulation. Secure smart contracts and cryptographic techniques can be employed to enable secure and verifiable energy trading. Protection against cyber attacks targeting energy infrastructure and secure communication channels are vital to maintain the resilience and security of blockchain-based energy solutions.
Decentralized Applications (DApps)
Security considerations in decentralized applications encompass smart contract security, user data privacy, and protection against vulnerabilities. Auditing and rigorous testing of smart contracts are necessary to identify and mitigate potential security flaws. Implementing secure access control mechanisms, encryption, and user data protection techniques help maintain user privacy. Ensuring the security of DApp platforms, including secure wallets, robust authentication mechanisms, and protection against common vulnerabilities, is essential to prevent unauthorized access and attacks targeting DApps and their users.
Smart Contract Security
Smart contracts, being a critical component of blockchain technology, require specific security considerations. Auditing and testing the code for vulnerabilities, such as reentrancy attacks or integer overflow/underflow, is essential to prevent potential exploits. Implementing access control mechanisms and proper input validation helps protect against unauthorized access and malicious input. Secure coding practices, code reviews, and regular updates to address newly discovered vulnerabilities are crucial to ensuring the security and integrity of smart contracts.
Consensus Algorithm Resistance
Consensus algorithms need to be resistant to various attacks, including denial-of-service (DoS) attacks, where an attacker floods the network with malicious requests to disrupt the consensus process. Implementing robust mechanisms to detect and mitigate DoS attacks, such as rate limiting or network congestion control, helps maintain the stability and security of the consensus algorithm. Additionally, protecting against timing attacks, where an attacker exploits the time taken for certain operations, is important to prevent potential vulnerabilities.
Immutable Ledger Integrity
The immutability of the blockchain ledger is a fundamental security feature. Ensuring the integrity of the ledger involves protecting against attacks that attempt to modify or manipulate previously recorded transactions. Techniques such as cryptographic hashing and digital signatures are employed to verify the authenticity and integrity of transactions. Implementing robust mechanisms to prevent unauthorized modifications, tampering, or collusion is crucial to maintain the trustworthiness and security of the blockchain ledger.
Key Management and Wallet Security
Key management and wallet security are vital components of blockchain security. Protecting private keys from unauthorized access and theft is essential to prevent unauthorized transactions. Implementing strong encryption, secure storage mechanisms, and multi-factor authentication can help safeguard private keys. User education and best practices for secure key management, such as offline storage or hardware wallets, are crucial to minimize the risk of key compromise and unauthorized access to blockchain assets.
Security Audits and Penetration Testing
Regular security audits and penetration testing are essential to identify vulnerabilities and ensure the robustness of blockchain systems. Independent security audits can assess the overall security posture, identify potential weaknesses, and recommend remediation measures. Penetration testing, conducted by ethical hackers, helps simulate real-world attacks to identify and address vulnerabilities before malicious actors exploit them. Continuous monitoring, updates, and proactive sec
Conclusion
Security considerations are of paramount importance when selecting and implementing consensus mechanisms in blockchain networks. Each consensus mechanism has its strengths and weaknesses, and understanding the associated security considerations is crucial for maintaining the integrity and trustworthiness of the blockchain ecosystem. By addressing these security challenges, blockchain technology can continue to evolve and provide secure and reliable solutions across various industries.





